Cloud Sovereignty Governance: Why This Topic Belongs in the Boardroom, Not the Server Room
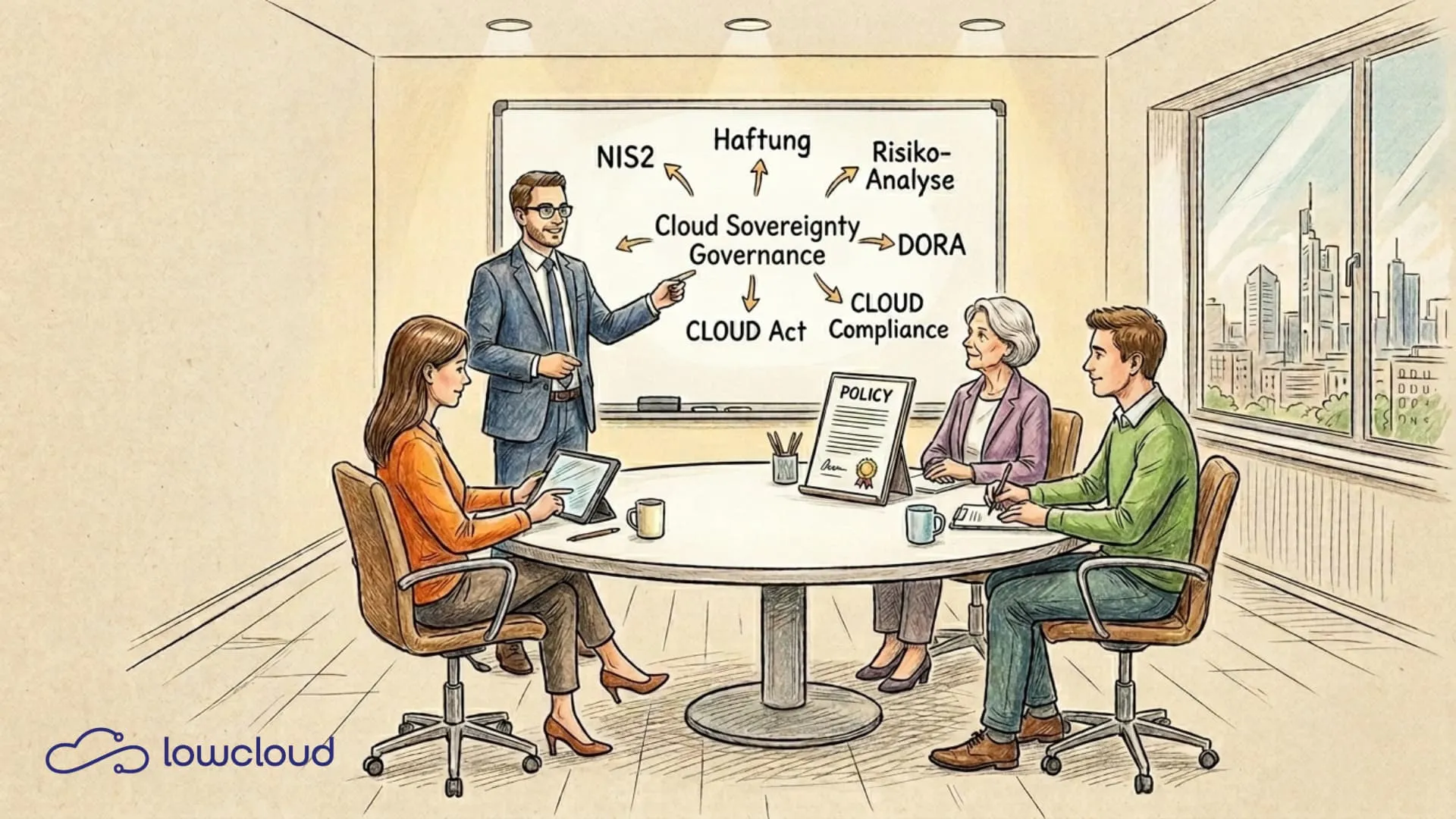
If you are still delegating cloud sovereignty to your IT lead in 2026, you have not understood the regulatory risk. NIS2, DORA, and growing geopolitical uncertainties make a demonstrable sovereign cloud policy mandatory. The responsibility lies not in the server room, but in the boardroom.
What Cloud Sovereignty Really Means in 2026
The misconception runs through many organizations: you host GDPR-compliantly, the data sits somewhere in Frankfurt, so you are sovereign. That is not true — data residency and data sovereignty are fundamentally different concepts.
Cloud sovereignty is more than data localization. It describes who actually has control over data, infrastructure, and access — and who does not. Three dimensions are critical:
- Data sovereignty: Who defines, classifies, and controls data usage (including key/rights management and data flows)?
- Operational sovereignty: Who operates the platform day-to-day, and who can technically enforce changes, admin access, or support access?
- Legal immunity: To what extent is the provider (corporate structure/legal jurisdiction) protected from extraterritorial access rights, or can exclude such access?
A detailed breakdown of these three concepts can be found in our Cloud Sovereignty Framework article. What sovereignty means technically, we described in our cloud vendor lock-in analysis.
A hyperscaler with a German data center can organizationally support data sovereignty and operational sovereignty, but legal immunity depends significantly on the provider's corporate structure and legal jurisdiction. And that is where it gets complicated.
The CLOUD Act (Clarifying Lawful Overseas Use of Data Act) allows US authorities to access data from US companies, regardless of where the data is physically stored. A data center in Munich does not protect you from a CLOUD Act request if the operator has a US parent company. This is not theory — it is current US federal law.
Why Many Companies Are Repositioning This Topic
Cloud sovereignty is no longer viewed as an IT project in many organizations, but as part of risk management — comparable to fire safety or compliance management. This is a paradigm shift, and it has concrete reasons.
The first reason is regulatory pressure. NIS2 has been transposed into German law since October 2024. DORA has been in effect since January 2025 for the financial sector. The Data Governance Act adds further obligations around data sharing and intermediation. All these regulatory frameworks require not statements of intent, but demonstrable measures including documented cloud governance.
The second reason is geopolitical. Recent years have shown that dependencies on non-European cloud infrastructures are a strategic risk. What sounded like an abstract scenario has materialized in concrete supply chain problems and political tensions.
The third reason is economic. Companies operating in the public sector or in sensitive B2B areas lose contracts if they cannot demonstrate a credible cloud sovereignty strategy. This is not a future scenario — it is happening today in procurement processes.
NIS2 and DORA: What Is Concretely Required of You
NIS2 targets companies in critical and important sectors: energy, transport, healthcare, digital infrastructure, financial services, and more. For a detailed breakdown of what NIS2 demands from DevOps teams technically, see our compliance guide. The requirements are specific:
- Risk analysis and documentation of IT security measures
- Demonstrable security policies for the use of cloud services
- Reporting obligations for security incidents
- Management liability — board members and managing directors can be held personally responsible
DORA goes even further for financial institutions. The Digital Operational Resilience Act requires comprehensive ICT risk management that explicitly covers cloud dependencies. Third-party contracts must contain exit strategies, critical service providers must be audited, and all of this must be documented and auditable.
What Is Missing in an Audit When No Policy Exists
Imagine a NIS2 audit. The auditor asks for your cloud governance documentation. You show your AWS contract. The auditor asks for the documented risk analysis regarding third-country access. You do not have one. They ask about the exit strategy. Also missing.
This is not a niche scenario. This is the reality in many mid-sized companies that use cloud services productively but have never developed a formal sovereign cloud policy. The consequences range from fines to personal liability of the management.
What a Sovereign Cloud Policy Must Contain
A sovereign cloud policy is not a 50-page rulebook. It is a clear, living document that answers five core questions:
1. Data Categorization and Localization Rules
Which data may reside in which cloud environments? Personal data, IP-sensitive data, and regulatory-relevant data require different treatment.
2. Provider Qualification
By what criteria do you select cloud providers? Provider's legal jurisdiction, certifications (BSI C5, ISO 27001, SOC 2), sub-processors. This must be defined and regularly reviewed.
3. Access Control and Monitoring
Who has access to production data? How is access logged? Are there technical measures against unauthorized third-country access (e.g., end-to-end encryption with self-managed keys)?
4. Exit Strategy
How do you migrate data and workloads if a provider fails or no longer meets your requirements? What timelines, formats, and costs are realistic?
5. Responsibilities and Review Cycle
Who is internally responsible for the policy? When is it reviewed? Which changes in the regulatory environment trigger a revision?
Why This Is Not a One-Person Decision
The CTO can be responsible for the technical implementation. But a sovereign cloud policy has dimensions that go beyond IT.
The CFO must understand the economic dependencies: What does a forced provider switch cost? What does a compliance violation cost? What does a data breach cost that resulted from missing sovereignty measures?
The Head of Legal / General Counsel must know the contract architecture: Which clauses in provider contracts are non-negotiable for DORA-compliant companies? Which third-country clauses are currently being silently accepted?
And the CEO or the board bears the ultimate responsibility. Under NIS2, explicitly and personally.
This is the real reason why cloud sovereignty is becoming a C-level issue: not because the topic is complex, but because liability is moving upward.
European Alternatives: What Matters in Provider Comparisons
The market for sovereign cloud solutions has developed significantly over the past two years. There are more options than in 2023, but also more ambiguity about what "sovereign" actually means for a provider.
Pay attention to the following criteria:
- Legal jurisdiction: Is the provider a European company without a US parent company?
- Operations: Are the data centers operated by the provider themselves or rented from a hyperscaler?
- Certifications: BSI C5 Type 2 is the relevant standard for the German market. ISO 27001 alone is not sufficient.
- Key management: Who controls the encryption keys? Do you have the option to use BYOK (Bring Your Own Key)?
- Contractual safeguards: Are there explicit clauses that exclude or make third-country access subject to documentation requirements?
First Steps: How to Start Today
You do not need to start with a complete policy document. But you need to start.
A pragmatic approach in three phases:
Phase 1: Inventory (2–4 weeks)
Map all cloud services in use. Note for each service: provider, legal jurisdiction, data class, contractual basis. This sounds trivial but is not documented in most companies.
Phase 2: Risk Assessment (2–3 weeks)
Identify the three to five most critical dependencies. Where would a forced switch hurt the most? Which services process the most sensitive data?
Phase 3: Policy Draft (4–6 weeks)
Write a first version of the sovereign cloud policy. Get legal feedback. Approve the document at management level. Schedule the first review date.
This is not a large project. It is a manageable process that must be actively initiated — preferably before the first NIS2 audit is on the calendar.
Cloud sovereignty is a leadership task, not an infrastructure question. The companies that understand this in 2026 will face audits with confidence and score points in procurement processes. The others will learn the hard way.
If you want to run sovereign Kubernetes workloads on a European DaaS platform (DevOps as a Service) that is designed from the ground up for data control and compliance, take a look at lowcloud. No dependency on US hyperscalers, no CLOUD Act risk, no hidden third-country transfers — a platform that technically implements your sovereign cloud policy, not undermines it.
What Is DevOps as a Service and When Does It Actually Make Sense?
DevOps as a Service sounds like yet another buzzword. But behind it lies a concrete model that can take real work off development teams, when applied correctly. This article explains what DaaS means, what a provider actually delivers, and where the limits of the model lie.
PaaS vs. DaaS: What
PaaS and DaaS often come up in the same conversation but mean fundamentally different things. One takes infrastructure off your plate, the other handles DevOps processes. Knowing the difference leads to better architecture decisions.