Avoiding Cloud Vendor Lock-in: What Real Sovereignty Means Technically
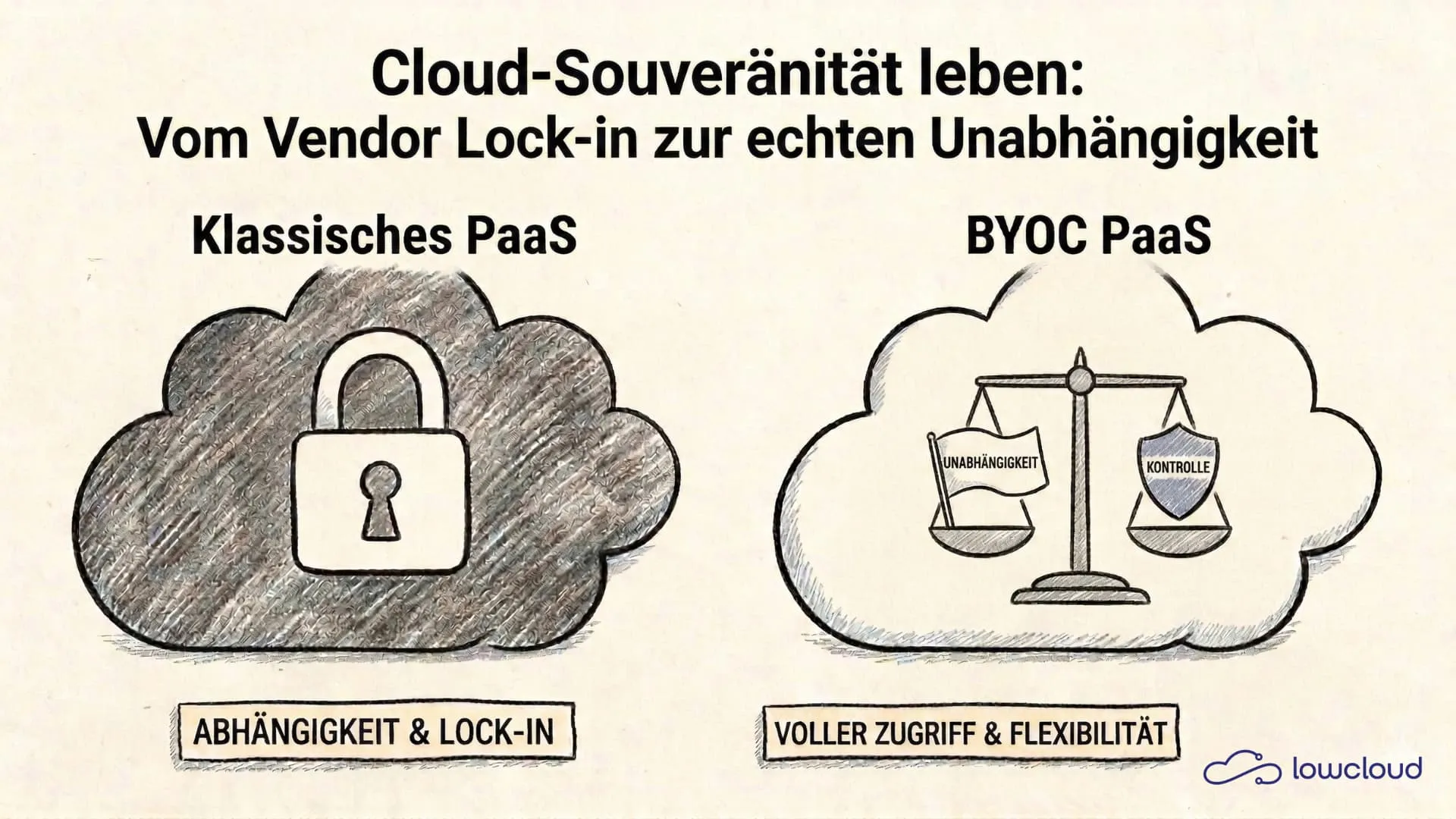
Vendor lock-in is the unspoken business model of many cloud platforms. Once you're deeply enough integrated, you don't switch anymore. Not because the tool is particularly good, but because switching is too expensive, too complex, and too risky. This article shows why that's not a law of nature, what avoiding cloud vendor lock-in actually looks like, and how lowcloud architecturally breaks this pattern.
What Vendor Lock-in Really Means
Most developers think of price increases first when they hear vendor lock-in. The provider doubles their rates, and you're stuck because migration would be too costly. That's real, but it's only the surface.
More Than Price Increases: Structural Dependency
Real lock-in goes deeper. It happens when the infrastructure your services run on doesn't belong to you. When your data sits on servers you have no direct access to. When your deployments are controlled through proprietary APIs that no other provider understands.
In this state, you're not a customer. You're a hostage.
Why Migration With Traditional PaaS Is So Expensive
With platforms like Heroku, Render, or Railway, your infrastructure runs on the provider's server accounts. You see a clean abstraction layer: push to Git, app runs. That's convenient. But when you want to switch because of prices, features, or a company shutting down, you start from scratch. A comparison of modern Heroku alternatives shows how widely this switching cost can vary.
Re-provision. Migrate data. Update DNS. Reconfigure all dependent services. That takes days to weeks and costs significantly during ongoing operations — migration costs, including substantial cloud egress fees, that are often missing from cloud TCO calculations. The EU Data Act now requires providers to actively reduce these barriers. The providers know this. And that's exactly why the model is so widespread.
How Traditional PaaS Platforms Structurally Lock You In
The fundamental problem is architectural: the provider holds the infrastructure. You pay for usage, but you own nothing.
With Heroku, for example, your dynos run on Salesforce servers. You can configure what runs on those dynos, but you can't access the underlying server, address it directly, or transfer it to another environment. Your databases? Also with the provider. Your add-ons, environment variables, build pipelines? All proprietary.
The same structure is found in most modern PaaS offerings. The deployment experience is excellent. The exit experience is not.
This is not an oversight. It's the model.
Cloud Sovereignty: What It Concretely Means Technically
Cloud sovereignty is a term widely used in the industry and rarely precisely defined. Usually it means: data storage in a specific country or with a specific provider. That's relevant, but not sufficient.
Real sovereignty means: you can switch your provider without jeopardizing your operations. You can shut down your provider without losing your applications. You have direct access to the infrastructure your services run on at all times.
Your Infrastructure, Your Account. The BYOC Approach
BYOC stands for Bring Your Own Cloud, or more specifically: Bring Your Own Account. The principle is simple: instead of a PaaS provider renting infrastructure for you and selling you access to it, you connect your own cloud account to the tool. The tool orchestrates your infrastructure on your account. It doesn't own it.
The difference is fundamental. You're not a tenant. You're an owner.
The "What Happens If" Test as an Architecture Criterion
A simple test for any cloud platform: what happens if the provider ceases to exist tomorrow?
With traditional PaaS models, the answer is uncomfortable: your services go down. You must migrate immediately. Under time pressure, without preparation.
With a BYOC model, the answer is different: the infrastructure keeps running because it belongs to you. You lose the orchestration tool, but you don't lose your operations.
This test is not an academic thought experiment. Startups die. Providers pivot. Prices rise. Those who align their architecture with this test sleep better.
How lowcloud Architecturally Eliminates Vendor Lock-in
lowcloud is built on this principle. Not as a marketing promise, but as a fundamental technical decision that shapes the entire product design.
Orchestration Instead of Hosting. What the Difference Is
lowcloud doesn't rent infrastructure for you. lowcloud orchestrates infrastructure on your account.
Specifically: you connect your Hetzner account to lowcloud, for example. lowcloud provisions servers there, configures Docker containers, sets up networks and databases. All on your account, with your credentials, in your infrastructure. lowcloud is the tool, not the owner.
This means:
- The servers are in your Hetzner account. You can access them directly at any time.
- The Docker containers and their configuration belong to you.
- Your databases run on servers in your account.
- You have full SSH access and direct control at all times.
This architecture is not a feature. It's an attitude: we want you to use the tool because it makes your daily work easier, not because you can't continue without us.
When You Shut Down lowcloud: What Happens and What Doesn't
This is the concrete test: you cancel your lowcloud account. What happens?
Your Docker containers keep running. Your databases are reachable. Your servers in your Hetzner account continue to exist. You lose the dashboard, automated deployments, monitoring, and the simple management interface, but you don't lose your applications.
You can access your servers directly via SSH and continue working manually. You can connect another tool. You can transfer the infrastructure to another management layer.
The transition requires effort. But it's possible, calculable, and can be planned under normal conditions, not as an emergency measure under pressure.
What This Means for DevOps Teams in Practice
For developers and DevOps teams, this approach concretely changes several things:
Full transparency over infrastructure. Anyone who can directly access the Hetzner account sees exactly what's running. No black box, no hidden network configurations, no "the platform manages that for you."
Emergency scenarios are plannable. A runbook for the case that lowcloud fails or is unreachable can be written. The infrastructure is known. The manual steps can be documented. With traditional PaaS models, this is often simply not possible.
Compliance becomes easier. Many industries have requirements about where data resides and who has access to it. When the infrastructure runs on your own account, these questions are easier to answer. You can prove that only you and nobody else has access to your production data.
No negotiation risk with price increases. When a provider doubles their prices, the reaction with BYOC is different. You can switch the orchestration tool without migrating the infrastructure. This fundamentally changes the negotiation position.
Less risk during growth. Those who grow don't want to discover at the wrong moment that their infrastructure is chained to a single provider. Making the right architectural decisions early costs little. Correcting them later costs a lot.
Conclusion: Simplicity and Independence Are Not Mutually Exclusive
The most common objection to BYOC approaches is: "That's more complicated." That's true for traditional self-hosting setups. For lowcloud, it's not.
The goal is for you to use a platform that gives you the simplicity of a modern PaaS. Deployments with a few clicks, automatic scaling, easy database connectivity, without giving up your independence. These two things are not contradictory when the product is built on this principle from the start.
Avoiding cloud vendor lock-in doesn't mean sacrificing convenience. It means getting convenience and control together.
lowcloud is built for teams that want to understand and control their infrastructure while still not having time to manage everything manually. If you want to know what this concretely looks like for your setup, you can try lowcloud directly and connect your own Hetzner or Kyberio account.
Cloud Sovereignty Framework: How the EU Is Finally Making Cloud Sovereignty Measurable
The new Cloud Sovereignty Framework provides the first structured, verifiable framework for what a cloud service must deliver to qualify as sovereign.
Digital Sovereignty with Kubernetes: When Is Open Source Truly Sovereign?
Kubernetes was created by Google. Yet European companies and government agencies use it as the foundation for their sovereign cloud strategy. This is not a contradiction, if you understand which dimension of sovereignty really matters.