Cloud Agnostic Architecture: Meaning and Trade-offs
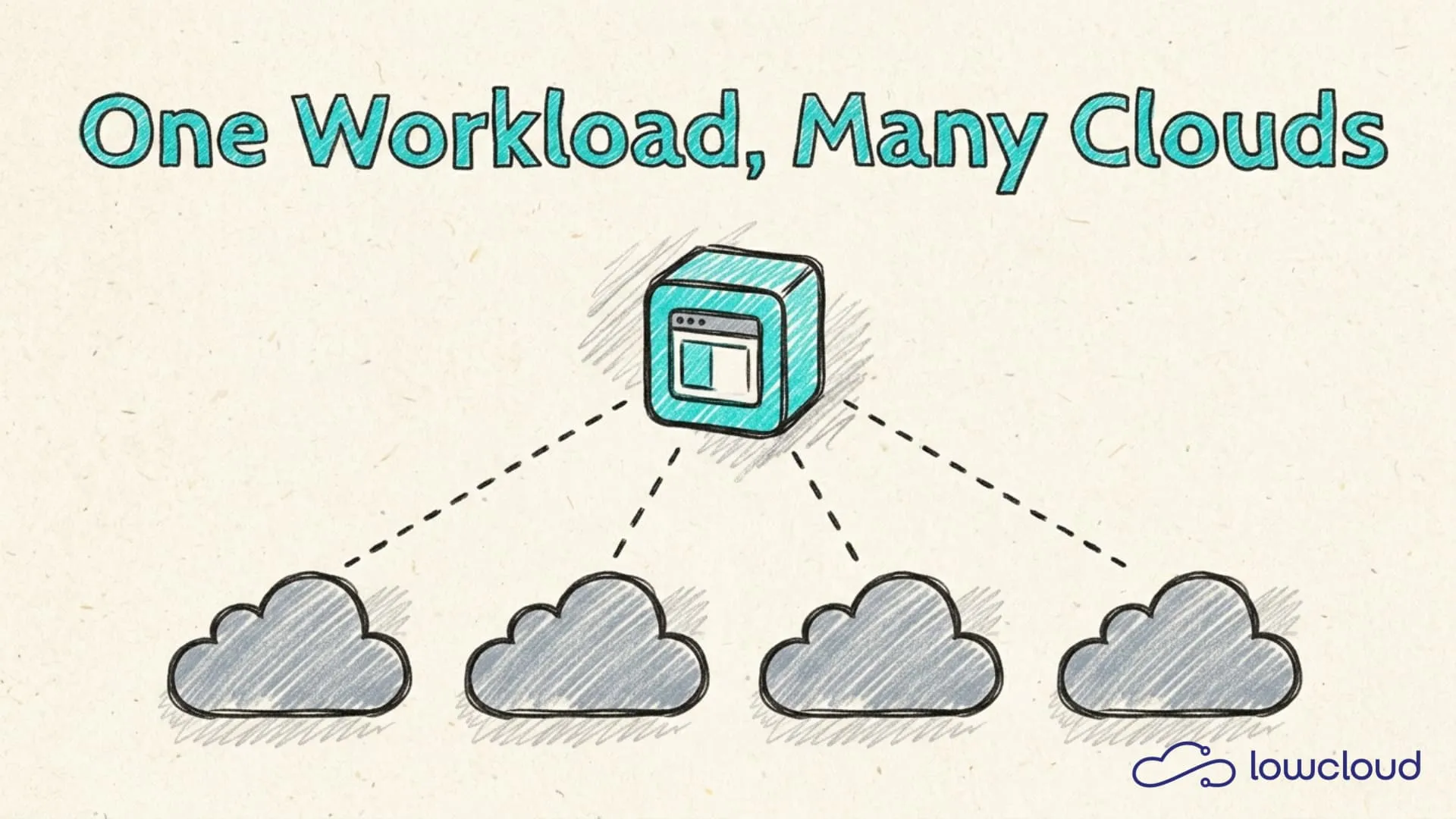
"Cloud agnostic" is one of those terms that comes up regularly in architecture reviews and technology discussions, often without anyone clearly explaining what it actually means. The underlying idea is neither complicated nor abstract. It is about designing software architecture and infrastructure so that it does not depend on a specific cloud provider. If you build cloud agnostically, you can run your workload on AWS, Google Cloud, Azure or your own infrastructure without having to fundamentally rewrite your codebase.
This matters for one simple reason. Once you have invested deeply in the services of a single provider, switching costs you. Not just money, but also time, regression testing and rewritten integrations.
What "cloud agnostic" actually means
Cloud agnostic describes a design philosophy. It is not a product, not a tool and not a magic layer that solves everything, but a decision that gets made at every architectural step. Do I rely on a standard that works everywhere, or on a managed service that only one provider offers?
In practice, this means using containers instead of provider-specific runtimes, standard databases instead of DynamoDB or Firestore, and open message brokers instead of SQS or Pub/Sub. This is not because proprietary services are bad, since they are often more convenient. It is because every step in that direction creates a dependency that will eventually come back to bite you.
The difference between cloud agnostic and multi-cloud
These terms are often confused or used interchangeably, but they are not the same.
Multi-cloud means that a company uses multiple cloud providers simultaneously, for example AWS for compute, GCP for machine learning and Azure for Microsoft workloads. This can happen for various reasons, such as better pricing, geographic availability or the technical strengths of individual providers.
Cloud agnostic is the prerequisite for multi-cloud to work smoothly at all. A cloud-agnostic architecture can be deployed across multiple providers without friction. An architecture that is deeply integrated with AWS-specific services is not cloud agnostic, even if it is theoretically distributed across multiple regions.
In short, multi-cloud is an operating model, while cloud agnostic is a design principle.
Where vendor lock-in really comes from
Lock-in rarely happens through a single large decision. It usually creeps in through small, pragmatic steps, each individually reasonable but collectively a problem.
The most obvious sources are provider-specific managed services such as AWS RDS with Aurora-specific features, Google Cloud Spanner or Azure Cosmos DB. Once you build on Spanner, you will not be reproducing that on another provider any time soon.
Less obvious but equally critical are several other areas. Serverless functions like AWS Lambda, Google Cloud Functions and Azure Functions share similar concepts but have different trigger systems, configuration formats and runtime environments, so code often cannot be transferred 1:1. IAM and permission models are another sensitive point, because anyone who builds their entire access management on AWS IAM faces the task of constructing a completely new permission model when switching providers. Proprietary networking services add to this, as VPC-specific configurations, load balancer setups and DNS management differ significantly between providers. The same applies to monitoring and logging, since deep investment in CloudWatch, Stackdriver or Azure Monitor does not migrate easily.
The invisible lock-in traps
Some services appear neutral at first glance but still create dependencies. Object storage is a good example. S3 is the de facto standard, but S3-compatible APIs have subtle differences. If you rely on S3-specific features like certain event types or lifecycle policies, you will only notice this during migration.
The same applies to Kubernetes distributions. EKS, GKE and AKS are all Kubernetes, but with different add-ons, network plugins and storage classes. Relying on these provider-specific details means your workload is not actually portable, even with Kubernetes underneath.
Kubernetes as the foundation for cloud-agnostic architectures
Kubernetes has established itself as the most practical common denominator for cloud-agnostic infrastructure. This is not just because it runs on every provider, but because the Kubernetes API itself is the standard. A Deployment, a Service or a ConfigMap works the same on EKS as on GKE, on a bare-metal cluster in a German data center, or on a local kind cluster.
This means that portability is largely guaranteed when workloads are consistently defined as Kubernetes resources and do not use provider-specific annotations or custom resources outside the Kubernetes standard.
Tools that enable portability
Kubernetes alone is not enough. A fully cloud-agnostic infrastructure requires a stack that also abstracts the infrastructure itself.
Terraform is the standard for Infrastructure as Code that works across providers. The same workflow can provision AWS, GCP and Azure resources, even if the provider modules differ.
Helm and Kustomize standardize the deployment of Kubernetes applications. Once packaged as a Helm chart, an application can be deployed to any cluster.
Crossplane goes one step further and brings cloud resources like databases or object storage into the cluster as Kubernetes custom resources, abstracting the underlying provider. Someone running a PostgreSQL instance via Crossplane on AWS today can provision the same resource on a different provider tomorrow without changing any application logic.
The Container Storage Interface (CSI) standard ensures that storage volumes can be mounted regardless of the provider. The same applies to the Open Container Initiative (OCI) format for container images.
Where cloud-agnostic architectures hit their limits
Portability is not free. Building consistently cloud-agnostically often means forgoing optimizations that a specific provider offers.
The clearest example is AWS Aurora, which is significantly faster than standard PostgreSQL on RDS for certain workloads. Not using Aurora to stay cloud agnostic means leaving performance on the table. The same goes for Google's BigQuery, since using standard OLAP tools does not automatically give you the same scale and performance.
The trade-off is real and should be made deliberately. For most use cases the difference is marginal. For highly specific, heavily optimized workloads it can be significant.
Another constraint is the abstraction overhead, which is non-trivial. A well-configured Crossplane setup, a clean Helm chart library and consistent IaC across multiple providers all cost effort to build and operate. For an early-stage startup primarily optimizing for time-to-market, this is often not the right focus. Being cloud agnostic is an investment that pays off in the long run.
Data sovereignty as a driver, especially in Europe
For European companies, cloud-agnostic architecture has a second, increasingly important dimension, namely data sovereignty.
The GDPR and sector-specific regulations like KRITIS or the NIS2 directive place clear requirements on where data may be stored and processed. Companies deeply integrated into the infrastructure of a US hyperscaler have little flexibility when new requirements force a different solution.
Cloud-agnostic architectures restore that flexibility. If an application runs on a standardized Kubernetes stack with no proprietary dependencies on a specific provider, moving to a European or sovereign cloud provider is not a reimplementation, but a deployment to a new cluster.
This is especially relevant for companies in the financial, healthcare and public sectors, but also for anyone who wants to keep their infrastructure independent of political and regulatory developments in the US in the long run. The connection between Kubernetes and digital sovereignty becomes particularly clear here.
How a PaaS platform puts provider independence into practice
The idea behind cloud-agnostic architecture is compelling, but implementation takes time and expertise. Anyone without a dedicated platform engineering team mastering Crossplane, Terraform and Kubernetes operations simultaneously will quickly hit capacity limits.
This is where a Kubernetes-based PaaS platform like lowcloud comes in. The platform abstracts the underlying cloud provider and gives development teams a unified interface, regardless of whether the workload runs on a German data center, a sovereign cloud provider or a hyperscaler. Deployments, monitoring, scaling and network configuration work identically.
The result is that teams work with Kubernetes-native workflows without having to deal with provider-specific details. And when requirements change, whether regulatory, economic or technical, switching providers is an operational decision and not an architectural crisis.
Data Governance Act: What SMBs and DevOps Teams Need to Know
The EU Data Governance Act affects technical teams too. Learn what the DGA means for your Kubernetes deployments, data flows, and infrastructure choices.
Kubernetes Migration: What You Need to Know Before You Start
A successful Kubernetes migration requires solid preparation. Learn the most common mistakes, a step-by-step approach, and when a PaaS is the better choice.