Minimalist Cloud Architecture: Why Less Complexity Means More Stability
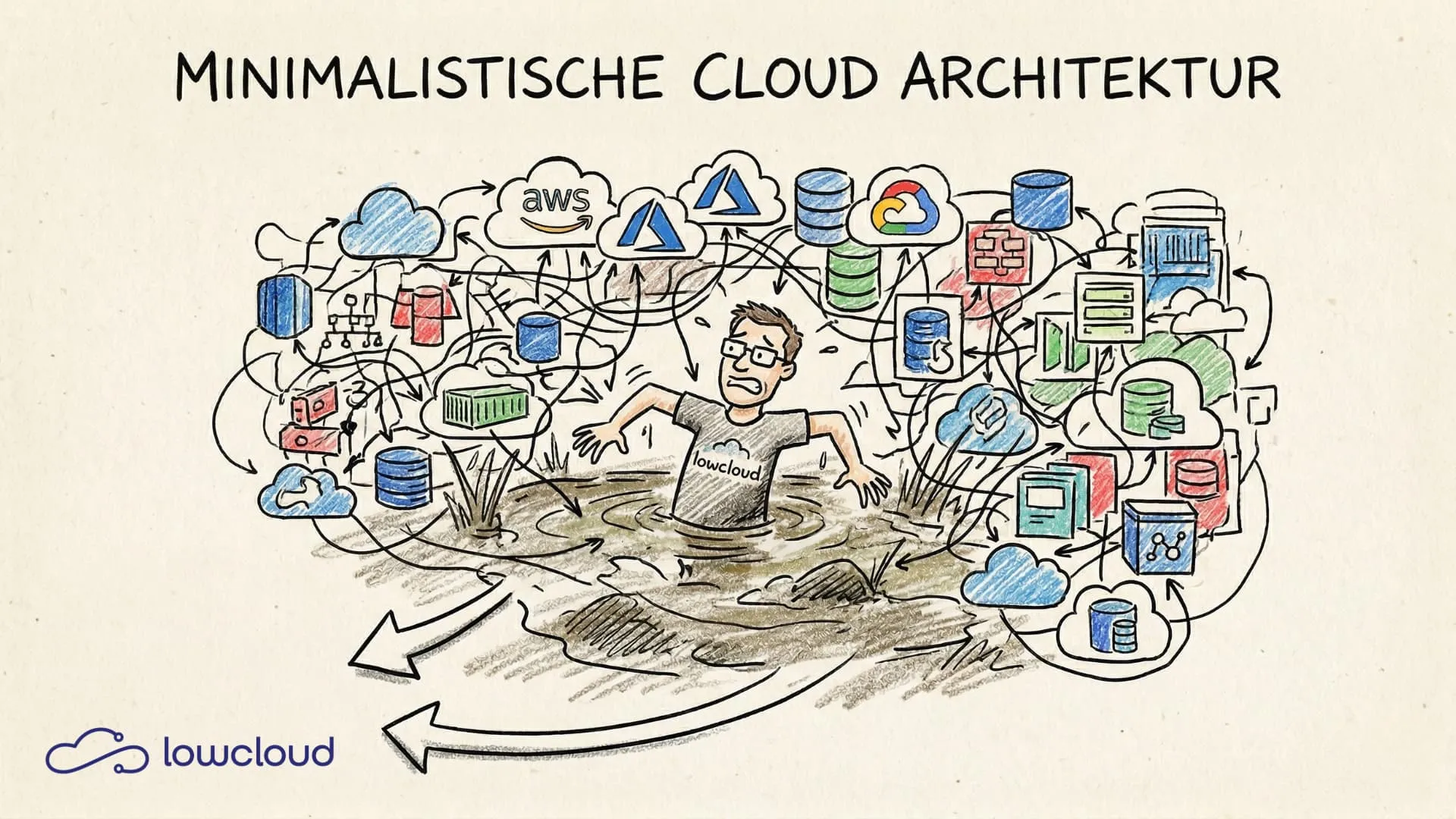
A Kubernetes cluster with eight different operators, three separate service mesh implementations, and a CI/CD pipeline that nobody can understand without documentation. This isn't an extreme example – it's the norm at many companies that migrated to the cloud over the past few years. The problem isn't the technology. It's the unspoken assumption that more components equal more capability.
Minimalist cloud architecture flips that assumption on its head.
Complexity Is Not a Sign of Maturity
There's a well-documented reflex in development teams: when a new technology exists and solves a real problem, it gets adopted – even when the existing problem is already solved. The result is infrastructure born from a genuine desire to do things well, but whose operational burden eventually outweighs every other benefit.
Complexity has real costs that show up in daily work:
- Longer incident response times. When five systems are involved in a single request, troubleshooting takes five times as long.
- Difficult onboarding. New team members need weeks to understand what's actually happening.
- Cognitive overhead. Anyone working with ten different abstractions every day makes more mistakes.
- Growing security attack surface. Every additional component is a potential attack vector.
The difference between good and bad architecture isn't the number of technologies in use. It's whether every component delivers clearly measurable value that justifies its maintenance cost.
What Minimalist Cloud Architecture Actually Means
Minimalism in the cloud doesn't mean giving up scalability or running a single container on a single server. It means deliberately deciding which parts of a system are truly needed – and leaving out the rest.
That sounds trivial. In practice, it's hard, because leaving things out requires active decisions, while adding things is usually the path of least resistance.
The Principle of Minimal Footprint
Every component in an architecture must answer one question: what happens if we remove it? If the answer is "not much" or "we're not sure," that's a signal. A good architecture review asks exactly these questions on a regular basis – not during the initial design, but every few months, because systems change and components that were necessary yesterday may be redundant today.
In concrete terms, this means:
- No sidecar that doesn't deliver actively used data
- No operator whose custom resources nobody on the team touches daily
- No managed service whose added value can't be translated into reduced operational effort
Managed Services: Simplification or Hidden Complexity?
Managed services are often marketed as the solution to complexity. That's sometimes true. A managed database service eliminates backup management, patching, and failover configuration. That's real simplification.
But managed services can also just shift complexity around. When a team uses five different managed services, each with its own configuration language, monitoring endpoints, and IAM concepts, the overall system is more complex than before – even though each individual component is "managed." The question isn't "managed or self-hosted?" but "does this simplify our overall operations?"
Kubernetes and the Tendency to Bloat
Kubernetes as a platform is flexible enough to support nearly any architectural decision. That's both a strength and a problem. The flexibility tempts teams into solving everything at the infrastructure level, even when the solution actually belongs in the application or the process.
Common patterns that make Kubernetes setups unnecessarily complex:
Operator inflation. There's an operator for every database, every message broker, and every monitoring tool. Each operator brings its own custom resource definitions, its own RBAC rules, and its own update cycles. Ten operators mean ten potential sources of conflict and ten separate update processes -- a Kubernetes-specific form of DevOps tool sprawl.
Sidecar overload. Service meshes like Istio or Linkerd inject sidecar containers into every pod. That brings mTLS, traffic management, and observability – but also double the resource consumption and an additional layer that needs to be configured, updated, and debugged. For many teams, the effort-to-benefit ratio is unfavorable.
Custom controller sprawl. Once teams start writing their own Kubernetes operators, maintenance effort grows exponentially. Every custom controller is code that needs to be maintained – usually by the same people building the actual application.
Practical Patterns for Lean Clusters
A few principles that make a real difference in practice:
Simplify your namespace strategy. Many teams work with dozens of namespaces that provide barely any additional isolation but multiply the RBAC configuration. Fewer, clearly delineated namespaces with well-defined boundaries work better.
Keep ingress configuration minimal. A single ingress controller with standardized annotations is sufficient for most workloads. Specialized routing hidden across hundreds of different ingress objects makes debugging unnecessarily difficult.
Set resource defaults. Instead of giving every deployment definition individual resource requests and limits, LimitRanges and ResourceQuotas at the namespace level work more cleanly and reduce copy-paste errors.
What Minimalist Architecture Delivers in Practice
The benefits of a leaner architecture don't show up immediately, but they're measurable.
Stability. Fewer components mean fewer possible causes of failure. In a system with five parts instead of fifteen, the probability of two components having issues simultaneously is significantly lower. That sounds trivial, but it has real impact on availability.
Shorter incident response. When an alert fires and the team has the entire architecture in their head, troubleshooting takes minutes instead of hours. Observability data is clearer, trace data is less noisy, and the number of possible causes is smaller.
Easier onboarding. New developers who can understand an architecture in half a day become productive faster. That has a direct impact on team capacity – especially in growing teams or those with frequent turnover.
Smaller security attack surface. Every running process, every exposed service, every network connection is a potential attack vector. A minimalist architecture has structurally fewer of them. On top of that, fewer components also mean fewer CVEs that need regular patching.
Lower operating costs. This is often the most convincing point for decision-makers: fewer running services mean less compute cost, fewer license fees for managed services, and less time spent on maintenance.
When Complexity Is Justified
Minimalism isn't an absolute principle. There are situations where complexity is unavoidable – and it would be dishonest to pretend otherwise.
Multi-region deployments with active-active configuration are complex because the problem is complex. Database replication across regions, conflict resolution for distributed write operations, and network latency management can't be defined away.
Systems with strict compliance requirements – in finance or healthcare, for example – sometimes need audit trails, encryption layers, and access controls that simpler systems don't require.
The difference is: in these cases, complexity is a direct consequence of a real requirement. Every team should be able to answer, for every architectural decision, which requirement drives it. If the answer is "because we might need it someday," that's not a good reason.
The Platform Approach as a Structural Answer to Complexity
One of the core problems with Kubernetes infrastructure in growing organizations is that complexity gets distributed. Every team running Kubernetes workloads has to deal with ingress, RBAC, resource management, monitoring configuration, and deployment processes. This leads to inconsistent setups, duplicated work, and varying security standards across teams.
A platform approach solves this problem structurally: instead of letting each team manage its own infrastructure complexity, a shared platform pulls these concerns upward and provides them in a standardized way. Teams deploy applications – they don't configure the same ingress controller for the twentieth time.
This is the core of what lowcloud is built on: a Kubernetes DevOps-as-a-Service platform that centralizes infrastructure complexity so development teams can focus on their applications. If you want to see what this looks like in practice, the lowcloud platform offers concrete answers to the question of how to simplify Kubernetes operations without losing control.
Minimalist cloud architecture isn't a trend or a counter-proposal to modern cloud practices. It's the consequence of recognizing that every component has a cost – even when it's not currently causing problems. Those who regularly question what's truly needed build systems that work better in the long run.
Zero-Config Kubernetes: Why Simplicity Wins
Kubernetes configuration costs teams hours every day. How zero-configuration approaches with sensible defaults simplify deployments and boost productivity.
Software Deployment for SMBs: How Small Teams Ship Faster
How small teams move from manual deployments to automated workflows using CI/CD, PaaS, and GitOps — without building a platform team.