Simplify Kubernetes Configuration: The Path to Human-Readable Cloud
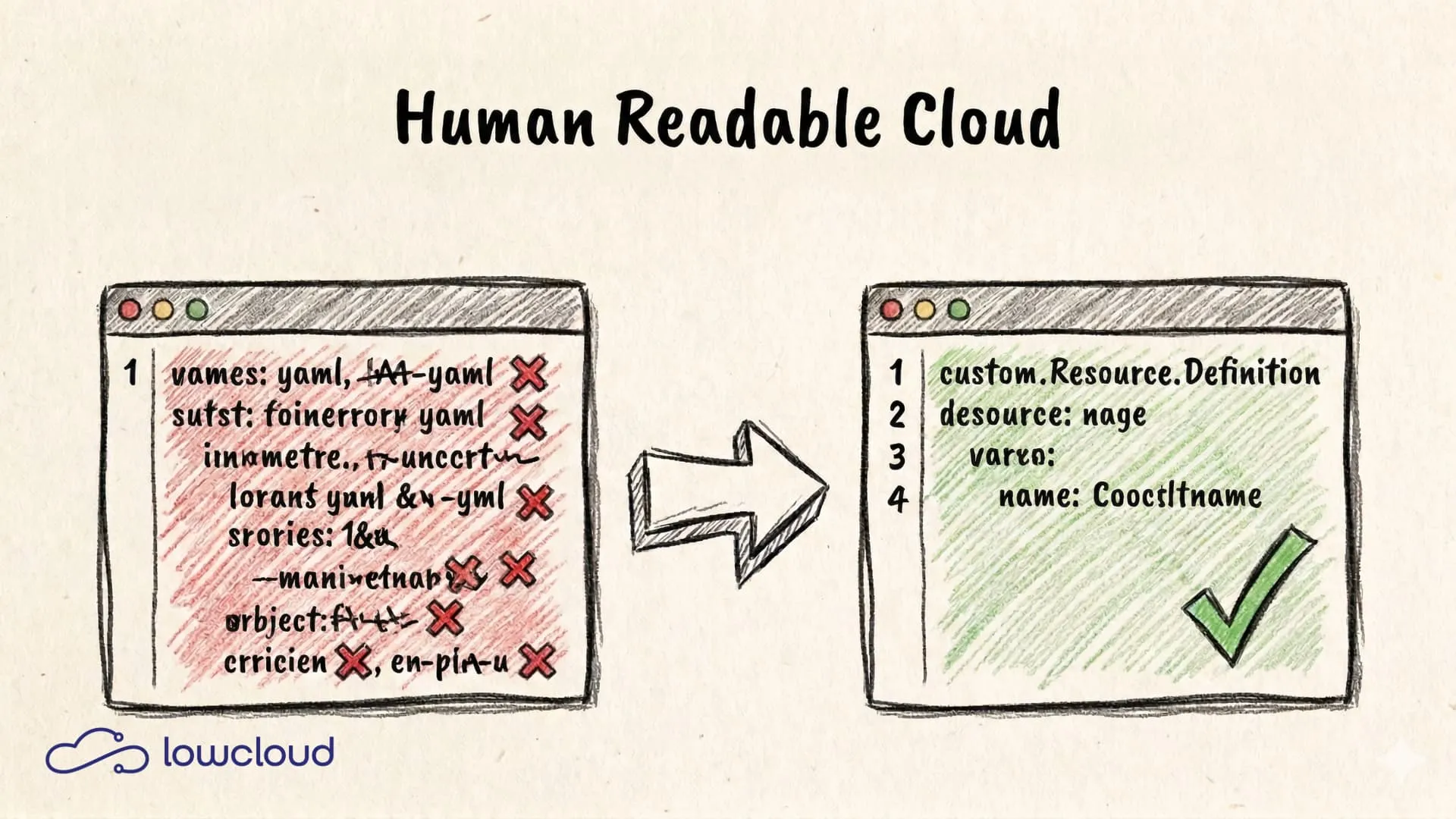
If you've ever debugged a Kubernetes deployment error in a 300-line YAML file, you know: the problem isn't Kubernetes itself — it's how we talk to it. A wrong indentation, a missing hyphen, a label that doesn't match somewhere, and the pod won't start. The gap between what a platform can do and what a developer understands isn't an immutable fate. It's a solvable engineering problem.
Why YAML Is the Problem, Not Kubernetes
YAML became the standard configuration format in Kubernetes because it's more human-readable than JSON. That's true for small files. With real Kubernetes infrastructure, that readability ends quickly.
The fundamental issue: YAML is a serialization format, not a configuration language. It has no types, no comment formats for validation, no built-in abstractions. Anything beyond flat key-value pairs becomes unwieldy. Kubernetes doesn't help: the API has grown organically, different resource types have inconsistent structures, and the same logical intent — "start this application with three instances" — requires different fields and nesting levels depending on context.
The Most Common YAML Error Classes in Kubernetes
- Indentation errors are invisible and lead to syntax errors that only surface during
kubectl apply - Type errors:
"true"(string) vs.true(boolean) — both valid in YAML, but interpreted differently by Kubernetes - Copy-paste errors in namespaces, labels, or selector definitions that silently slip through
- Deprecated API versions:
apps/v1beta1has long been deprecated but still appears in many guides
None of these errors are due to human failure. They are structural consequences of a format that wasn't built for this use case.
What "Human-Readable" Actually Means
"Human-readable" isn't a marketing term for "less YAML." It's a design property: a configuration is human-readable when someone who understands the domain (i.e., Kubernetes, cloud deployments, microservices) can immediately read and verify the intent behind a configuration without having to look up the schema first.
This doesn't mean configuration has to be simple or short. A CRD that describes a PostgresCluster with a field replicas: 3 is human-readable, even if an operator underneath generates dozens of YAML resources. The developer sees what they want; the system knows how to implement it.
Human-readable configuration is fundamentally domain-oriented — it speaks the language of the problem, not the language of the implementation.
Simplifying Kubernetes Configuration: The Key Approaches
There's no universal answer, but there is a spectrum of proven approaches.
Helm — Templating with Pitfalls
Helm is the most widely used package manager for Kubernetes. For a practical example, see how to deploy PostgreSQL with Helm. Charts allow you to write parameterizable YAML templates controlled by values.yaml. For reusability of deployment definitions, Helm works well.
The problem: Helm templates are Go templates with YAML content. As soon as the logic gets more complex — conditionals, loops, nested values — the templates themselves become unreadable. Anyone who has debugged - if .Values.ingress.enabled with three levels of indentation and an - end somewhere below knows what this means.
# Example: A typical Helm template fragment
- if .Values.autoscaling.enabled
apiVersion: autoscaling/v2
kind: HorizontalPodAutoscaler
metadata:
name: include "myapp.fullname" .
spec:
minReplicas: .Values.autoscaling.minReplicas
- end
Helm solves the distribution problem, not the readability problem.
Kustomize — Overlays Instead of Templates
Kustomize takes a different approach: no templating, but structured patches. A base configuration is adapted through overlays for different environments (dev, staging, prod). The advantage: the base remains valid YAML, and overlays are surgical modifications.
Kustomize works well for manageable environment variations but hits its limits when configurations become more complex or when the differences between environments are large.
CRDs and Operators — Domain-Specific APIs
Custom Resource Definitions (CRDs) are the most powerful tool for readable configuration. They allow you to define your own Kubernetes resource types — and thus your own domain-specific API.
An operator that responds to a PostgresCluster resource can generate all necessary Deployments, Services, PersistentVolumeClaims, and ConfigMaps from it. The developer writes:
apiVersion: postgres-operator.crunchydata.com/v1beta1
kind: PostgresCluster
metadata:
name: my-database
spec:
instances:
- replicas: 3
backups:
pgbackrest:
repos:
- name: repo1
volume:
volumeClaimSpec:
accessModes: ["ReadWriteOnce"]
resources:
requests:
storage: 10Gi
It's not perfectly readable yet, but it describes what is desired — not how it's technically implemented. The operator handles the rest. This pattern is the foundation for real abstractions in Kubernetes.
Platform Engineering as the Answer
Individual tools solve individual problems. Platform Engineering as a discipline solves the overarching problem: how do you build an internal developer platform that enables developers to use cloud resources without being Kubernetes experts?
The answer lies in abstraction layers. Platform Engineering teams define the abstractions — which resource types exist, which parameters developers may set, what is configured by default. Development teams work against these abstractions, not against raw Kubernetes YAML.
Tools like Crossplane go particularly far: with Composite Resources, you can define cloud-agnostic abstractions that provision AWS, GCP, or Azure resources under the hood. A developer describes an AppDatabase; the Composite Resource Controller handles provider-specific details.
What Makes a Good Abstraction
A good abstraction:
- hits the right level — neither too low (then it's just a thin layer over YAML) nor too high (then necessary configuration options are missing)
- has stable defaults that fit the most common use case — a principle we explore in depth in our article on zero-config Kubernetes
- offers escape hatches when standard defaults aren't sufficient
- is internally consistent — the same concepts are expressed the same way
An abstraction is bad when it introduces new complexity that is greater than what it solves. Many internal platform projects fail precisely because of this: they hide YAML behind a proprietary DSL that nobody knows and for which there's no tooling support.
Simplifying Kubernetes Configuration in Practice: A Realistic Path
The shift from raw YAML to readable configuration doesn't happen overnight. A sensible path:
1. Take inventory: Which Kubernetes resources are currently maintained manually? Where do the most errors occur? Which parts are most frequently copied and adapted?
2. Identify candidates: Resources that repeat often and are always structured the same way (deployments for microservices, similar database setups) are good candidates for abstraction.
3. Choose your tool: For package reuse: Helm. For environment variations based on stable manifests: Kustomize. For true domain-specific APIs: CRDs with an Operator or Crossplane. For a complete internal platform: Backstage as the frontend, Crossplane or custom Operators as the backend.
4. Start small: An abstraction for a clearly defined problem (e.g., "how do we deploy a microservice") is more valuable than a half-finished platform framework. Iterating is easier when the foundation works.
5. Incorporate developer feedback: The target audience is developers who work with the platform daily. Their feedback about what they understand, what confuses them, and what they're missing is more important than technical elegance.
Common pitfalls:
- Abstractions that internally generate YAML that nobody can debug anymore
- Platform teams that don't have the capacity to maintain the platform — creating a new legacy system
- Premature generalization: abstractions built for problems that aren't yet understood will be built wrong
How lowcloud Positions Itself and Concretely Relieves Teams
Many teams feel the problem before they can name it: Kubernetes is powerful, but its user interface (manifests, tool combos, expert knowledge) scales poorly with team size and daily demands. This is exactly where lowcloud positions itself: as a "digital DevOps" — a platform-oriented alternative to the classic "build your own Internal Developer Platform" strategy.
lowcloud targets teams that want (or need) to use Kubernetes but don't have the time or people to permanently build, operate, and harden a platform. As a DevOps-as-a-Service provider, lowcloud delivers exactly this operational relief.
What this means in practice:
- Less decision and tool chaos: Instead of a growing collection of Helm charts, Kustomize overlays, CI scripts, and "this is how we do it here" wiki pages, there's a consistent path.
- Standardization without lock-in: The platform delivers standards (security, updates, observability, deployments) — while leaving room for edge cases when they're technically necessary.
- Speed in the delivery funnel: Teams get from "runs locally" to "runs reliably in the cloud" faster, without every change turning into a Kubernetes debugging workshop.
- Operations as a product, not a project: Platform Engineering often becomes a never-ending project. lowcloud turns it into a product: standards, guardrails, and operational experience are built in and continuously maintained.
This means lowcloud supports exactly the migration described above: first bring order to repetitions, then introduce abstractions — without every team having to invent this platform work themselves and carry it long-term.
Conclusion
Simplifying Kubernetes configuration isn't a one-size-fits-all problem. It's a series of decisions about which complexity to hide, which to keep visible, and how to ensure the result remains maintainable. For the broader architectural perspective on why fewer components lead to more stability, see our guide to minimalist cloud architecture.
The common denominator of successful approaches: they separate what from how. Developers describe what they want. Platforms and operators handle the how. This isn't a new idea — it's the fundamental principle of every good abstraction. With Kubernetes, it just takes a bit more effort because the default interface happens to be YAML.
If you want to take this path for your team without starting from scratch: lowcloud is built on exactly this principle. The platform provides a managed Kubernetes environment where developers work through structured, readable interfaces — without being confronted with cluster configuration on a daily basis.
DevOps in SMBs: Why Missing Roles Become a Real Risk
SMBs without a dedicated DevOps role risk outages, knowledge loss, and technical debt. Learn why this happens and what actually helps.
Collaborative DevOps: How Modern Teams Build Cloud Apps Together
How shared ownership, GitOps, and platform engineering bridge the gap between development and operations for faster, more reliable deployments.